Meet Arca — the platform that replaces your logging stack and your security stack
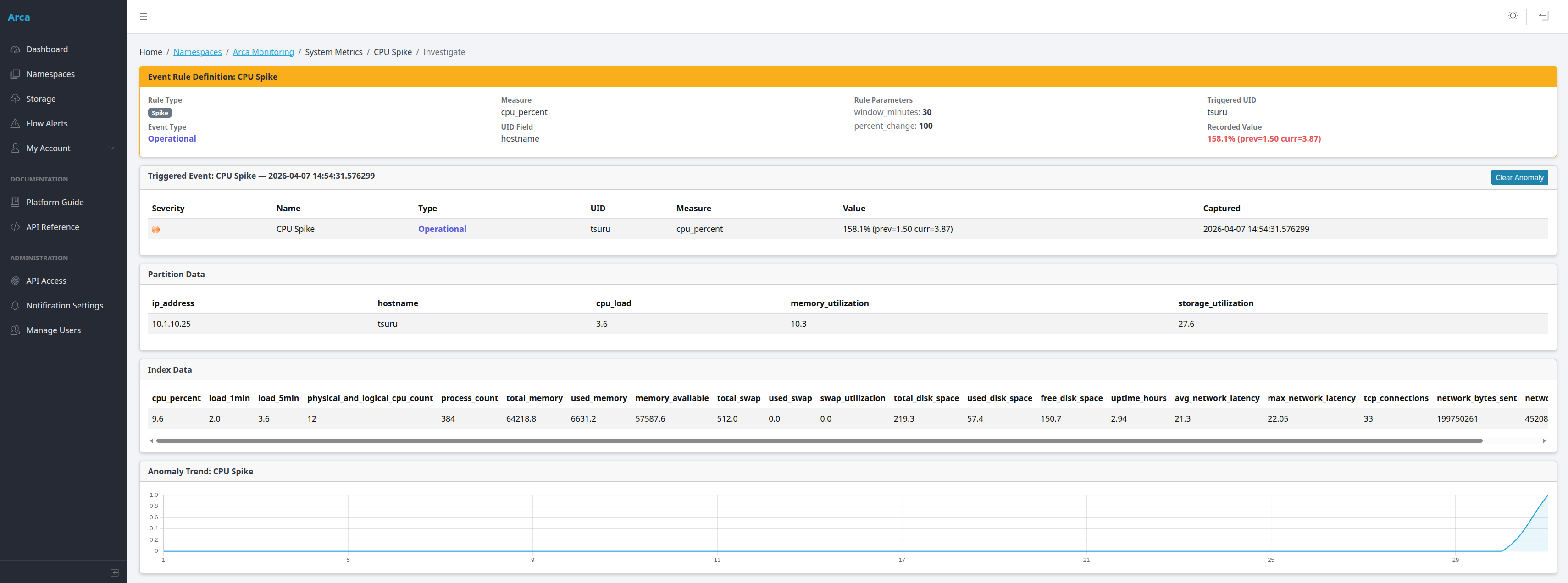
Arca is built AI-first from the ground up. Every rule trigger launches an autonomous AI investigation that identifies the attacker, maps to MITRE ATT&CK techniques, and recommends response actions. An embedded chat assistant at every collection and namespace level lets you investigate incidents in plain English. Backed by self-hosted deployment, 5-role RBAC, and no per-GB billing.